Nearshore healthcare development teams in Latin America cost 60-65% less than U.S. equivalents while delivering the real-time collaboration HIPAA compliance requires.
LATAM senior engineers cost $75,000-$105,000 fully loaded versus $220,000-$250,000 domestically. A five-engineer nearshore team saves $1.44 million over 24 months at 61.5% cost reduction. Brazil’s LGPD, Mexico’s LFPDPPP, and Colombia’s Law 1581 align structurally with HIPAA’s technical and administrative safeguards.
We connect HealthTech companies with pre-vetted engineers from Bogota, Medellin, Mexico City, Sao Paulo, and Buenos Aires. Each candidate is screened for HIPAA-awareness, English fluency, and U.S. work style fit. Below you’ll find HIPAA compliance requirements, country benchmarks, BAA essentials, and a six-step implementation framework.
What Is Nearshore Development for Healthcare?
Nearshore development sources engineering talent from geographically proximate countries. For U.S. healthcare companies, that means Latin America. It sits between onshore (same country, highest cost) and offshore (distant time zones, lowest cost but highest coordination friction).
Why Are Healthcare Organizations Turning to Nearshore Development?
Domestic talent acquisition has become structurally impaired. 85% of HealthTech firms report engineering vacancies unfilled for over 90 days (up from 42% in 2020). Average time-to-hire for a senior developer has stretched to 4.5 months. Year-over-year salary inflation for senior U.S. roles runs at 23%. HealthTech venture funding hit $15.3B in 2025, a 26.1% increase, concentrated in AI, admin infrastructure, and clinical decision support. Domestic-only hiring is no longer financially viable for growth-stage companies.
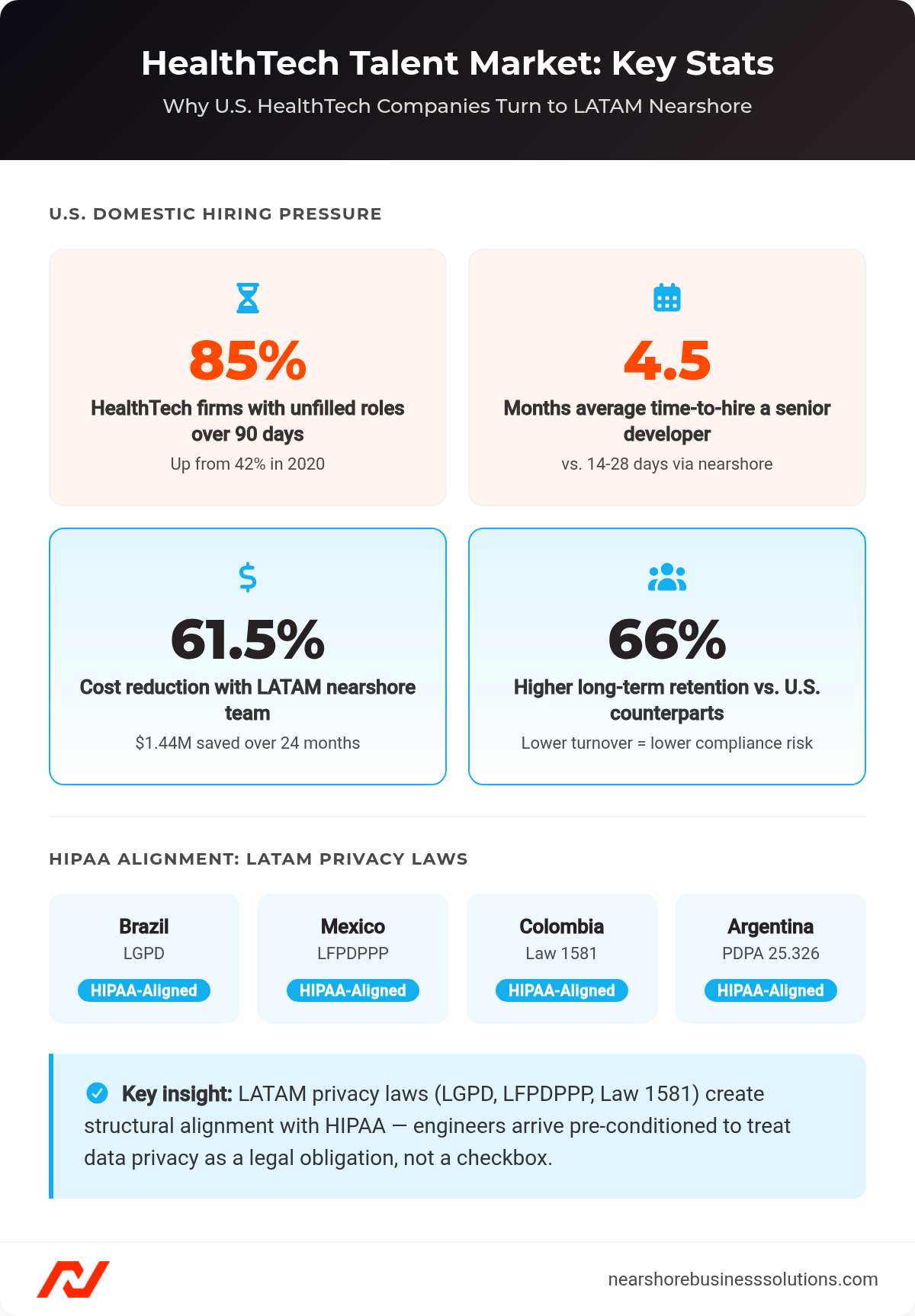
Key HealthTech talent market stats and LATAM privacy law HIPAA alignment by country.
How Does Nearshore Differ from Offshore and Onshore for Healthcare?
LATAM nearshore delivers 5-8 hours of daily overlap with U.S. teams. Offshore models in Asia or Eastern Europe create 12-hour time deltas, eliminating synchronous work entirely.
For healthcare, time-zone overlap matters operationally: real-time incident response, DevSecOps integration, morning standups, and afternoon sprint reviews are only viable with overlapping hours. Cultural alignment in LATAM reduces communication friction relative to offshore alternatives.
What Does HIPAA Compliance Require from Development Teams?
HIPAA imposes specific technical and administrative obligations on every person and system touching electronic protected health information (ePHI). For distributed teams, implementation requires deliberate architecture, not just policy acknowledgment.
What HIPAA Rules Directly Affect Software Development Practices?
The HIPAA Security Rule (Section 164.312) governs three specifications development teams must implement: audit controls, transmission security, and encryption.
- Audit controls (Section 164.312(b)): Require logging identity (who), action (what), object (which record), and context (timestamp, source IP, device posture)
- Transmission security (Section 164.312(e)): Mandates TLS 1.2 or higher for all web and API traffic
- The rule distinguishes required from addressable specifications. Addressable means implement unless a documented equally effective alternative exists
In practice, modern HealthTech treats encryption as mandatory even where technically “addressable.”
Who on a Nearshore Team Must Receive HIPAA Training?
Every person on the nearshore team must complete certified HIPAA privacy and security training before system access is granted. Expect 2-4 weeks for initial access and knowledge transfer. Full sprint velocity is typically reached within 3-6 months.
Reputable vendors make HIPAA training a standard pre-access requirement. Every engineer must hold a unique, non-recycled user identifier. Shared dev or admin accounts constitute a critical violation: they prevent forensic reconstruction during audits and eliminate accountability entirely.
When Is a Business Associate Agreement Required?
A Business Associate Agreement (BAA) is required before any nearshore contractor accesses systems that may contain patient data. For international partners, a standard BAA is insufficient.
The BAA must include:
- U.S. choice of law and forum selection (e.g., Delaware)
- Financial assurance: cyber liability insurance or a corporate guarantee
- Audit and inspection rights, with remote audits explicitly permitted
- Subcontractor accountability: the vendor must ensure downstream BAAs with all subcontractors
What Are the Benefits of Nearshore Development for Healthcare?
Three factors make LATAM nearshore compelling for HealthTech: cost savings of 60-65%, real-time collaboration parity with domestic teams, and structural alignment with HIPAA through LGPD-family privacy laws.
How Does Time-Zone Alignment Improve Healthcare Project Outcomes?
LATAM time-zone overlap resolves blockers 30% faster than asynchronous offshore models. Real-time incident response, continuous CI/CD security review, and sprint velocity all depend on synchronous collaboration. Offshore models structurally prevent this. A blocker raised at 4pm EST reaches an offshore team the following morning at the earliest.
Developers in Bogota (UTC-5) and Mexico City (UTC-6) deliver 7-8 hours of daily overlap with New York-based teams. That overlap enables same-day bug resolution and continuous DevSecOps review cycles that offshore models cannot match.
What Cost Advantages Does Nearshore Offer Over Domestic Healthcare IT Teams?
Domestic senior engineer total employer cost runs $220,000-$250,000 annually (base $140,000-$180,000 plus benefits, payroll taxes, equity, and recruitment). LATAM senior talent runs 60-65% lower.

5-engineer team cost comparison: U.S. domestic $2.34M vs. LATAM nearshore $900K over 24 months.
| Cost | |
|---|---|
| U.S. domestic team (5 engineers, 24 months) | $2,340,000 |
| Nearshore LATAM team (5 engineers, 24 months) | $900,000 |
| Savings | $1,440,000 (61.5%) |
Real-world benchmarks confirm the model: Gennev achieved 63% cost savings through nearshore DevOps modernization. A medical billing firm realized 68% payroll savings with zero security incidents over 18 months.
For a broader comparison of hiring software developers in Latin America, including engagement models and vetting standards, see our complete LATAM hiring guide.
How Does Cultural Alignment Reduce HIPAA Compliance Risk?
LATAM engineers operate under GDPR-inspired privacy frameworks: Brazil’s LGPD, Mexico’s LFPDPPP, Colombia’s Law 1581. This creates high structural alignment with HIPAA’s technical and administrative safeguards. Engineers arrive pre-conditioned to treat data privacy as a legal obligation, not an afterthought.
Retention amplifies this advantage. LATAM hires are 66% more likely to stay long-term versus U.S. counterparts. Lower turnover directly reduces compliance risk. Every new hire triggers a new onboarding and access provisioning cycle, each of which is a potential compliance exposure point.
What Are the Risks of Nearshore Development in Healthcare?
Four risks dominate HIPAA-distributed development: PHI in non-production environments, inadequate BAA provisions, missing anomaly detection, and reliance on VPN alone. Each is preventable with the right controls.
What Data Security Risks Come with Nearshore Healthcare Teams?
The most frequent HIPAA violation in distributed development is real patient data in staging or development environments. Copying a production database to staging constitutes both an impermissible disclosure and a failure to manage security risks. The fix is automated data masking enforced as a hard gate in the CI/CD pipeline, not a manual process.
Other high-probability failure modes:
- Insider snooping: Contractors accessing records without business necessity violates the minimum necessary principle
- Unpatched remote endpoints: A single vulnerable laptop can provide a lateral movement foothold for ransomware
- Lost or unencrypted devices containing cached PHI or API secrets are reportable breaches under the Breach Notification Rule
How Do Cross-Border Data Transfer Laws Affect HIPAA Compliance?
Each LATAM country imposes its own transfer controls on health data. BAAs must address these requirements jurisdiction-by-jurisdiction, not generically.
- Colombia (Law 1581): Receiving country must provide an “adequate” level of protection
- Mexico (LFPDPPP): Requires specific contractual protections and a formal Privacy Notice before data collection
- Brazil (LGPD): Classifies health data as “sensitive personal data” requiring explicit consent and mandates appointment of a Data Protection Officer (DPO)
What Happens if a Nearshore Vendor Suffers a PHI Breach?
U.S. courts have limited authority over foreign entities with no U.S. physical presence or assets. If a nearshore contractor triggers a breach, the U.S. covered entity remains 100% liable for OCR fines and remediation costs regardless of where the breach originated. Maximum penalties: HIPAA at $1.9M per year; Brazil’s LGPD at $10M per violation. This is precisely why BAA financial assurances and U.S. forum selection are non-negotiable provisions.
Which Countries Are Best for Nearshore Healthcare Development?
Latin America dominates for U.S. HealthTech due to time-zone alignment, GDPR-inspired privacy laws, and a maturing senior engineering talent pool. Pre-vetted nearshore platforms can deliver a shortlist in 72 hours and close a hire in 14 days.
What Nearshore Regions Have Strong Healthcare IT Regulatory Alignment?
- Brazil (LGPD): Data minimization aligns directly with HIPAA’s minimum necessary rule. Best for scale and AI/ML expertise. Engineers from Universidade de Sao Paulo (USP) lead the region in senior developer density. DPO appointment required.
- Mexico (LFPDPPP): Mirrors HIPAA’s administrative and technical safeguards. Engineers from Tecnologico de Monterrey are accustomed to rigorous documentation. Best for West Coast time sync.
- Argentina: High senior engineer density and strong English proficiency. Universidad de Buenos Aires (UBA) produces Latin America’s highest-rated developers. USD-denominated contracts required due to currency volatility.
- Colombia: The “Habeas Data” constitutional principle produces engineers who treat patient privacy as a fundamental right. Developers from Universidad de los Andes and EAFIT in Medellin’s Ruta N innovation district lead the region in compliance culture.
- Costa Rica: Premium pricing reflects a mature, U.S.-aligned tech ecosystem. Best suited for roles requiring senior-level autonomy.
What Are Senior Engineer Compensation Benchmarks Across LATAM?
LATAM senior healthcare engineers cost $75,000-$115,000 fully loaded versus $220,000-$250,000 domestically. The savings range from 54% to 66% depending on country and specialization.
| Role | Mexico | Brazil | Argentina | Colombia | Costa Rica |
|---|---|---|---|---|---|
| Backend Engineer | $85,000 | $80,000 | $75,000 | $78,000 | $95,000 |
| DevSecOps / SRE | $95,000 | $92,000 | $88,000 | $90,000 | $105,000 |
| AI / ML Specialist | $105,000 | $100,000 | $95,000 | $98,000 | $115,000 |
For backend developer and full-stack developer hiring guides with vetting standards specific to each role, see our role-specific pages.
How Do LATAM Data Privacy Laws Compare to HIPAA?
| Feature | HIPAA | LGPD (Brazil) | LFPDPPP (Mexico) | Law 1581 (Colombia) |
|---|---|---|---|---|
| Health Data Status | Regulated Category | Sensitive Category | Sensitive Category | Sensitive Category |
| Explicit Consent | Context-dependent | Mandatory | Mandatory | Mandatory |
| DPO Required | No (Privacy Officer) | Yes | Yes | No |
| Max Penalty | $1.9M/year | $10M/violation | 320k x Min Wage | 2k x Min Wage |
How Do You Build a HIPAA-Compliant Nearshore Team?
Building a compliant nearshore team requires six sequential steps. Each step is a dependency for the next. Skipping or reordering them is where most compliance failures originate.
Step 1: How Do You Define PHI Access Scope Before Onboarding?
Implement Role-Based Access Control (RBAC) before onboarding begins. Document which roles require access to ePHI versus synthetic or masked data environments. This step determines the blast radius if any single credential is compromised.
Step 2: How Do You Vet Vendors Against HIPAA Baselines?
Minimum vetting standards include: CEFR B2/C1 English proficiency, automated coding assessments for security-aware practices (SQL injection prevention, input validation), architecture interviews evaluating cloud-native security, and background checks covering national criminal records, global sanctions lists (FBI, Interpol, OFAC), and academic credential verification.
Step 3: What Must a Business Associate Agreement Include?
Execute BAAs before any work begins. The BAA must obligate the vendor to ensure subcontractors sign downstream BAAs with equivalent protections. Require cyber liability insurance or a corporate guarantee. U.S. choice of law is mandatory.
Step 4: What Technical Safeguards Must You Implement Across Remote Environments?
Four safeguards are non-negotiable for remote healthcare development: Full Disk Encryption (FDE) with remote-wipe capability on all engineer endpoints; automatic session logoff after 15 minutes of inactivity; immutable, append-only audit log repositories (e.g., AWS S3 with Object Lock); and HashiCorp Vault for centralized secrets management using dynamic, ephemeral credentials.
Step 5: When Does HIPAA Training Occur in the Onboarding Process?
All nearshore personnel complete certified HIPAA privacy and security training as a hard prerequisite to system access. Expect 2-4 weeks for initial system access and knowledge transfer. Full sprint velocity is typically reached within 3-6 months.
Step 6: How Do You Maintain Ongoing HIPAA Compliance?
Deploy real-time anomaly detection configured to alert on mass record exports, after-hours access, and unusual login locations. Centralize logs capturing identity, action, object accessed, timestamp, source IP, and device health posture. These logs are your primary evidence in an OCR investigation.
What Technical Safeguards Must Nearshore Healthcare Teams Maintain?
The six build steps above establish safeguards at onboarding. The specifications below define the ongoing technical standards those safeguards must meet. These are the requirements auditors will test against.
What Encryption Standards Apply to PHI Handled by Remote Developers?
TLS 1.2 or higher is mandatory for all web and API traffic, with no exceptions. Field-level encryption for ePHI at rest is required (disk-level encryption alone is insufficient). HIPAA treats encryption as effectively mandatory in modern HealthTech even where technically “addressable.”
How Should Access Controls Be Structured for Nearshore Teams?
Three controls define compliant access management for distributed healthcare teams. First, unique, non-recycled user identifiers for every engineer: shared accounts are a critical violation. Second, Just-In-Time (JIT) access for break-glass emergency procedures, with automatic revocation after a defined window. Third, HashiCorp Vault dynamic, ephemeral credentials that expire after use, eliminating persistent access paths.
HashiCorp Consul enforces mutual TLS (mTLS) and identity-based authorization between microservices, adding a second layer of access control at the service level.
How Is Multi-Factor Authentication Enforced Across Distributed Teams?
Phishing-resistant MFA integrated with SSO providers (e.g., Okta) is the baseline. Zero-Trust Architecture (ZTA) replaces static IP-based firewalls with dynamic identity verification: “never trust, always verify” regardless of network location. Zero-Trust Network Access (ZTNA) is preferred over traditional VPN. VPNs grant implicit trust to any device inside the tunnel. ZTNA verifies identity and device posture continuously.
How Do You Manage HIPAA Compliance Across an Ongoing Nearshore Engagement?
Ongoing HIPAA compliance in a distributed healthcare team requires three operational layers: formal periodic audits, continuous automated monitoring, and a documented incident response plan.
How Often Should HIPAA Compliance Audits Occur with Nearshore Partners?
Conduct formal security audits annually at minimum, with quarterly access reviews and continuous automated monitoring between cycles. BAAs must include the contractual right to conduct these audits, with remote audits explicitly permitted.
SOC 2 Type II is the standard attestation framework. It provides audited evidence of operational security controls over a 6-12 month period: ongoing attestation rather than a point-in-time snapshot.
What Does an Incident Response Plan Look Like for a Distributed Healthcare Team?
A functional incident response plan for nearshore teams requires three operational components working in parallel.
- Break-glass workflows granting temporary elevated access during outages, with automatic revocation after a defined window
- Continuous device posture checks verifying antivirus status, OS patch level, and encryption at each access attempt, not just at onboarding
- SIEM-based centralized access logging enabling full forensic reconstruction during breach investigations
How Do You Handle Employee Turnover on a Nearshore HIPAA Team?
Secrets management via ephemeral credentials (HashiCorp Vault) ensures departing engineers leave zero persistent access. Credentials expire automatically. There is no manual revocation step to miss. Combined with LATAM’s 66% higher long-term retention rate versus U.S. counterparts, turnover-driven compliance exposure is structurally lower than domestic alternatives.
What Certifications Should a Nearshore Healthcare Vendor Hold?
SOC 2 Type II and ISO 27001 are the baseline attestation standards for HIPAA-adjacent vendor evaluation. Neither is a HIPAA substitute; both are evidence of the operational discipline required to support it.
How Do SOC 2 Type II and ISO 27001 Complement HIPAA Compliance?
SOC 2 Type II provides time-bound, audited evidence of operational security controls over 6-12 months. ISO 27001 provides a global framework for information security management. Prioritize both when assessing vendor maturity.
What Evidence Should You Require from a Vendor During a Compliance Audit?
Demand documented evidence across five areas before granting any system access: a SOC 2 Type II report (review audit dates and scope carefully, stale reports are a red flag); ISO 27001 certification; HIPAA training records for the entire workforce (not just leadership); background check scope covering criminal records and global sanctions (OFAC, Interpol, FBI); and the full subcontractor BAA chain.
How Does Nearshore Compare to Offshore for HIPAA Projects?
Managed nearshore achieves near-parity with U.S. in-house teams on most HIPAA risk dimensions. Unmanaged offshore presents maximum exposure across every dimension.
| Risk Dimension | U.S. In-House | Managed Nearshore | Unmanaged Offshore |
|---|---|---|---|
| Endpoint Security | High Control | High (via Vendor MDM) | Low / Variable |
| Jurisdictional Risk | Minimum | Moderate (via BAA) | Maximum |
| Communication Sync | Real-time | Real-time | Delayed (12 hrs) |
| Access Logging | Native | Centralized (SIEM) | Often Fragmented |
| Culture of Privacy | High | Emerging / High (LGPD) | Low / Variable |
Frequently Asked Questions About HIPAA-Compliant Nearshore Development
These are the most common questions HealthTech CTOs and VPs of Engineering ask about nearshore healthcare development.
How Long Does It Take to Hire a Nearshore Healthcare Developer?
Pre-vetted nearshore platforms deliver a shortlist in 72 hours and close a hire in 14-28 days. U.S. domestic hiring for a senior healthcare engineer averages 4.5 months. System access and knowledge transfer add 2-4 weeks after hire.
What Happens if a Nearshore Developer Does Not Work Out?
Reputable nearshore vendors include a 90-day replacement guarantee. During the replacement period, the vendor provides a qualified interim engineer to maintain sprint continuity. Ephemeral credentials (HashiCorp Vault) ensure departing engineers leave zero persistent access automatically.
Does Our Company Need to Provide Equipment to Nearshore Engineers?
Enterprise-grade nearshore vendors provide all hardware: encrypted laptops with Full Disk Encryption (FDE), remote-wipe capability, and continuous device posture checks. You define the security baseline. The vendor enforces it at the endpoint level.
How Do You Pay LATAM Healthcare Developers?
Payments flow through the nearshore vendor using USD-denominated contracts in most LATAM countries. Argentina requires USD-denominated agreements due to currency volatility. Employer of Record (EOR) services handle local payroll compliance in each jurisdiction, eliminating the need for a local legal entity.
Do We Need a Local Legal Entity to Hire in Latin America?
No. Employer of Record (EOR) services provide compliant hiring in days rather than months. The EOR handles local payroll taxes, benefits, and labor law compliance in each LATAM country. You maintain full technical management of the engineers.
What Is the Difference Between Nearshore and Offshore for Healthcare?
Nearshore delivers 5-8 hours of daily overlap with U.S. teams. Offshore creates 12-hour time deltas, eliminating synchronous work entirely. For healthcare, same-day incident response and continuous DevSecOps review cycles require synchronous overlap. Offshore structurally prevents both.
Is a BAA Required for Every Nearshore Engagement?
Yes. A BAA is required before any nearshore contractor accesses systems that may contain patient data. The BAA must include U.S. choice of law, financial assurances, remote audit rights, and subcontractor BAA requirements. Accepting a standard vendor contract without these provisions leaves the covered entity fully exposed.
Is Nearshore Development Right for Your HIPAA-Compliant Healthcare Project?
The talent shortage is structural, not cyclical. With 85% of HealthTech firms unable to fill engineering roles within 90 days and salary inflation at 23% year-over-year, domestic-only hiring is fiscally unsustainable for growth-stage companies.
The financial case is board-defensible: a five-engineer nearshore team saves $1.44 million over 24 months at 61.5% cost reduction, while delivering real-time collaboration parity with in-house teams.
The compliance case is equally strong. LATAM’s GDPR-aligned privacy frameworks (LGPD, LFPDPPP, Law 1581) create structural regulatory alignment with HIPAA that offshore markets cannot match. Engineers from universities like Tecnologico de Monterrey, Universidad de los Andes, and UBA arrive pre-conditioned to treat data privacy as a legal obligation.
The companies that win in HealthTech over the next decade will build global engineering teams with the operational precision and HIPAA accountability the market demands. Nearshore is the most viable path to do so at scale.
Ready to Build Your HIPAA-Compliant Healthcare Engineering Team?
Nearshore Business Solutions sources and vets developers from Bogota, Medellin, Mexico City, Sao Paulo, and Buenos Aires. We screen for technical skills, English fluency, and U.S. work style fit. Our acceptance rate is 16%.
Every placement includes a 90-day replacement guarantee. You receive pre-vetted candidates in 2-4 weeks.
Get a free consultation to discuss your hiring needs and receive a custom quote.

